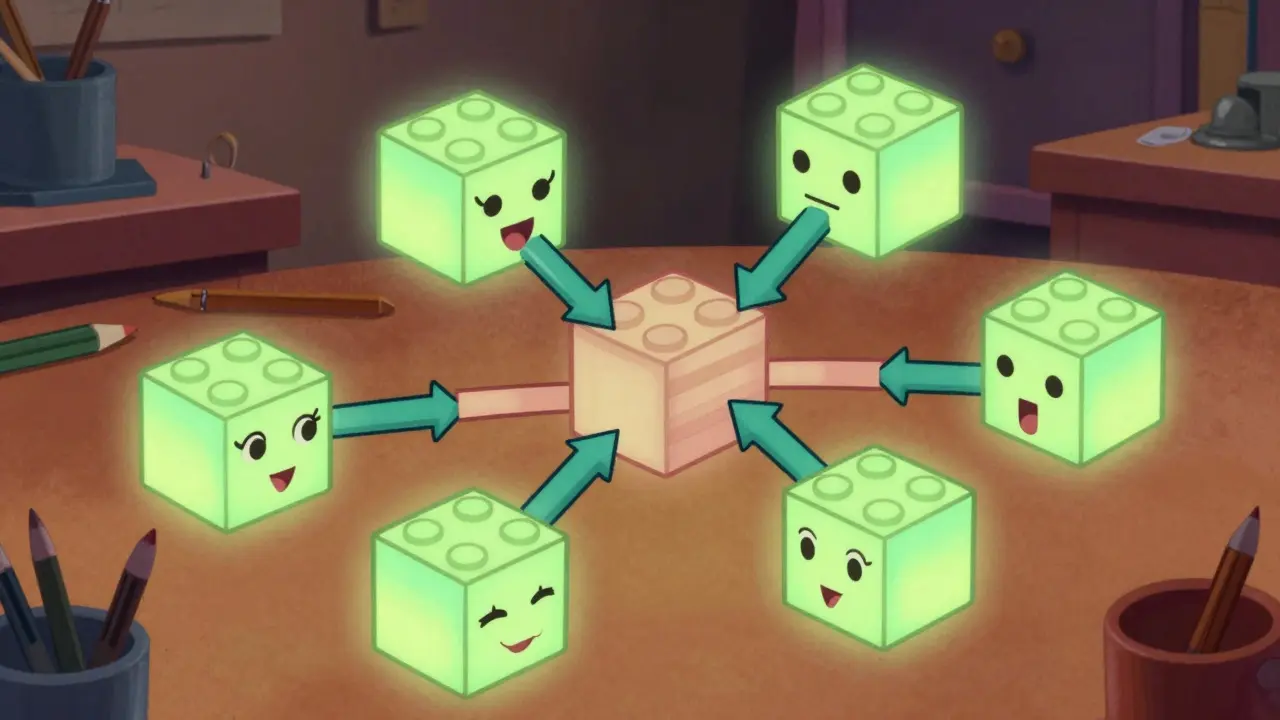
Imagine you are building a house using bricks made of concrete. Now imagine those bricks can actually talk to each other and form their own walls whenever you pile them up. That’s exactly what Smart Contract Composability allows us to do in the blockchain world. Instead of rebuilding the foundation every time you want to add a room, you just snap pre-made, secure components together. This isn’t just a nice-to-have feature; it’s the engine driving massive innovation in decentralized finance today.
If you’ve spent any time coding on a blockchain, you know the frustration of writing code for features that someone else already perfected. Why rewrite a lending protocol when one exists? Composability answers that question by turning software into open APIs that anyone can plug into. We’re past the days where every developer had to code their own bank from scratch. Now, we assemble banks, exchanges, and markets by snapping verified contracts together.
The Three Pillars of Composable Design
Not every smart contract can fit into this Lego-like ecosystem. To work together seamlessly, these digital contracts follow three non-negotiable rules. Without them, the system breaks down, and vulnerabilities appear.
First is Modularity. Think of modularity as specialization. Each contract does one job really well. A token standard like ERC-20 handles balances. It doesn't worry about swapping tokens-that's for a different contract. If you try to force a single contract to manage governance, trading, and staking simultaneously, you create a tangled mess that’s hard to upgrade and harder to audit. When contracts stay modular, you can pull one out and replace it without collapsing the whole application.
Second is Autonomy. This is about independence. A composable contract shouldn't crash because its neighbor went offline. It executes based on the data available on the chain, not on a server controlled by a third party. When you call an external function, you aren't hoping a centralized API stays up; you are invoking code that lives immutably on the Ethereum Virtual Machine. This ensures that even if the original creators of a token vanish, the asset remains usable in other applications.
Third is Discoverability. You can't compose something if you can't find it. The beauty of public blockchains is transparency. Anyone can query the code. Tools exist that index these functions, making it easy for developers to spot which libraries they can reuse. If a contract hides its logic behind private keys or obfuscated code, it fails this test. True composability relies on open-source defaults.
Why Traditional Software Fails Here
When you develop web apps in traditional environments, integration often involves handshakes and permissioning. You request access, set up API keys, and hope the documentation matches reality. If the provider changes their pricing model or shuts down your account, your app stops working. Smart contract composability removes the middleman entirely.
In the old world, if you wanted to integrate payment processing, you relied on Stripe or PayPal. They could delist you. On a blockchain, Decentralized Finance (DeFi) protocols provide functionality without requiring approval. A wallet connects to the chain, checks the contract, and interacts directly. This creates a "money lego" effect where money moves through multiple systems atomically-meaning it either completes fully or reverts completely, eliminating transaction gaps.
| Feature | Traditional APIs | Composable Contracts |
|---|---|---|
| Availability | Centralized servers can go offline | Always accessible via node networks |
| Censorship | Provider can revoke access | Censorship-resistant execution |
| Data Ownership | Siloed within company databases | Publicly verifiable on-chain |
| Integration Cost | Requires API keys and legal review | Permissionless calls via wallets |
Real-World Standards Driving Innovation
We don't need theory to see this working. Look at Uniswap. They built an automated market maker (AMM). Because their code was composable, other projects like Aave integrated it directly. Users could borrow assets against liquidity positions without leaving the Aave interface. You didn't need to manually move funds between platforms; the smart contract did it in one transaction.
Consider the role of standards themselves. ERC-20 became the gold standard for fungible tokens. But it wasn't the only path. Non-fungible tokens, governed by ERC-721, allowed unique assets like art to live on-chain. Later, ERC-1155 solved batch transfer issues. These standardized interfaces meant marketplaces like OpenSea didn't have to write custom code for every new collection. They built once, supported many. This reduced overhead significantly.
Security Risks in Complex Systems
Everything has a trade-off. High composability means high attack surface area. When contracts connect deeply, a vulnerability in one can cascade through others. We saw this with flash loan attacks. Malicious actors borrowed large sums, manipulated the price of an oracle, drained liquidity, and repaid the loan-all in seconds.
To mitigate this, rigorous testing is mandatory. Static analysis tools scan the code before deployment. However, the biggest risk isn't bad code; it's bad assumptions. If a stablecoin contract assumes an external liquidity source won't fail, it creates hidden fragility. The industry is moving towards "circuit breakers" in code that pause interactions if parameters look suspicious.
Cross-Chain Evolution
By 2026, being limited to a single blockchain is a constraint of the past. Interoperability protocols now allow Ethereum smart contracts to talk to Layer 2 solutions and sidechains seamlessly. This expansion requires robust bridging standards to ensure assets aren't lost during transfers. The core principles remain: modularity allows chains to specialize, autonomy keeps execution local, and discoverability tracks assets across networks.
Frequently Asked Questions
What makes a smart contract composable?
For a contract to be composable, it must rely on public interfaces (like ERC standards), maintain autonomy (run independently of centralized servers), and adhere to modular design (one specific function per contract) so it can interact safely with other protocols.
How does composability benefit developers?
It accelerates development by allowing teams to use existing, audited code rather than rewriting basic functions. This saves time and reduces security risks since foundational logic is reused from proven sources.
Is cross-chain composability safe?
It introduces new risks related to bridges and verification layers. Security depends heavily on the reliability of the interop protocol used. Always verify bridge audits before transacting across chains.
What is the relationship between Uniswap and Aave?
These protocols demonstrate deep composability. Aave users can use their liquid assets from Uniswap LP positions as collateral for loans, creating complex financial strategies in a single transaction.
Do legacy software architectures support this?
No. Traditional silos prevent this level of integration. Legacy systems require permissions and API keys, whereas blockchain standards allow anyone to interact with the code directly.

Justin Garcia
March 29, 2026 AT 15:48This whole concept is just marketing fluff designed to sell more tokens.
Lisa Walton
March 31, 2026 AT 03:16Oh wow, finally someone explains that magic internet money works like legos instead of explaining how nothing actually works. Surprising that nobody noticed the bricks explode halfway up the wall sometimes. We are told modularity fixes everything but vulnerabilities still leak everywhere. The optimism is almost cute given the track record of actual failures.
Shubham Maurya
April 1, 2026 AT 23:00Bro this is fire honestly 🔥 The way we snap contracts together is crazy good vibes. Everyone needs to see this for themselves. Why struggle when you can plug in verified stuff easily 🚀. The security part is real tho. Still feels like we are winning big 💎
Ashley Stump
April 3, 2026 AT 10:56Don't trust the bridge guys they always steal funds.
Addy Stearns
April 5, 2026 AT 02:29True composability requires a fundamental shift in how we perceive ownership itself. We spend too much time discussing technical standards rather than philosophical implications. When code becomes money, the abstraction layers blur significantly. Developers often ignore the human element embedded in these protocols. They assume autonomy means independence from society. That is a dangerous misconception for anyone building infrastructure. The risk lies in assuming digital immutability equals social permanence. Society evolves faster than any hard fork can accommodate changes. We need to consider the governance structures surrounding these tools. A modular contract can still execute a tyrannical outcome if parameters are set poorly. Transparency does not necessarily guarantee ethical behavior from operators. We see evidence of this in centralized exchanges hiding behind decentralized fronts. Real innovation comes from aligning incentives with community welfare. Otherwise we just create automated versions of predatory banking systems. The technology is sound but the philosophy driving adoption remains flawed today. We must look deeper at the social contract inherent in every function call.
Cara Boyer
April 5, 2026 AT 14:43It is clear the government wants us to rely on their tech but teh blockchain is actually a trap. You think you are free but the algoritm tracks evrything. Don't let them trick you into using the wrong standards because they control the data. The real freedom is offline and far away from these networks.
joshua kutcher
April 6, 2026 AT 07:30I find it encouraging to see people thinking about structural integrity in this space. It takes a village to build these things securely and sharing knowledge helps everyone stay safe. We should focus on education so more developers understand the risks involved here. Your points about testing are absolutely vital for progress. I hope we can continue supporting each other as we build this future.
Sean Carr
April 6, 2026 AT 19:43You've got some solid points there and I want to help you refine them further. Make sure you check your dependencies before deploying anything live though. Testing isn't optional when real money is on the line right now. Keep pushing the boundaries of what is possible with open source tools. You got this and the team supports you fully.
Disha Patil
April 8, 2026 AT 05:33But what if the code just breaks and no one knows why it happened then. It scares me when people say it is secure because it never stays that way. I feel like we are running into walls we cannot see coming soon.
Shaira Vargas
April 9, 2026 AT 12:37This makes me so sad to read because people lose everything constantly. We need more protection for our savings please do not let them hurt us. I am worried about the security part of this conversation today.
Michael Nadeau
April 9, 2026 AT 14:49The argument regarding transparency holds weight in theory but fails in practice when obfuscation hides malicious intent within standard libraries. We must remain vigilant about verifying sources before integration occurs. Trustless does not mean trustworthy in all contexts involving financial loss. Careful review prevents catastrophic failure modes later on down the line.
Alex Kuzmenko
April 9, 2026 AT 16:54i agrre with u on this point completely. its imp to verify the bridge audit reports before doing anything. dont get scammed pls. stay safe.
Beverly Menezes
April 11, 2026 AT 05:44We should all try to work together and share info safely. There is no reason to fight when we can learn from each other instead. Let us focus on positive growth and safety for the network.
Samson Abraham
April 12, 2026 AT 13:03agreed the risk assessment is thorough. we should prioritize security above convenience always. this system demands discipline.
Joy Crawford
April 12, 2026 AT 13:44wow this is scary and i agree with the fear factor <3 but we must move forward slowly. dont rush into losses please. stay safe out there friends 💖
Jay Starr
April 13, 2026 AT 07:51The drama surrounding failed contracts is exhausting to watch unfold daily. People scream about losses while blaming the tools instead of their own choices. It creates a chaotic environment where trust is eroded by sensationalism constantly.
Zackary Hogeboom
April 14, 2026 AT 09:30Hey great breakdown of the pillars here everyone. It really helps to see modularity explained like this for new devs. I think we can collaborate better on standards moving forward. What do you all think about the cross chain part specifically? Let's keep talking more about solutions.
Ronald Siggy
April 15, 2026 AT 18:43You need to take responsibility for your own due diligence regardless of the standard used. Stop waiting for someone else to fix your security gaps personally. Assertive action protects assets better than passive reliance ever could. Stand firm on audit results before deployment occurs.
Tiffany Selchow
April 17, 2026 AT 01:51Why bother making it easy for outsiders when our local nodes are superior anyway. These global standards dilute our control over critical financial infrastructure entirely. We should prioritize domestic chains over international open protocols immediately.
Markus Church
April 17, 2026 AT 22:47While the theoretical framework is robust, practical implementation faces significant hurdles regarding latency and fee structures. One must consider the economic viability of such frequent interactions at scale. Interoperability adds complexity that may outweigh benefits in certain niche applications currently.
athalia georgina
April 19, 2026 AT 04:26it feels like im the only one seeing the hidden danger here. you dont know what happens when they change teh rules behind ur back. i try to warn peopel but no one listens to the warnings.
Lisa Walton
April 20, 2026 AT 05:30Back to square one because the industry loves pretending legacy problems are solved by new buzzwords. Modularity helps until it doesn and then we rebuild everything from scratch again. Progress looks suspiciously like a repeating cycle of hype and disaster. Someone pass the popcorn while we wait for the next exploit.